Adversary Emulation: Mimicking a real-world cyber attack
Learn how to perform red team adversary emulation exercises end-to-end
4.65 (24 reviews)

388
students
4.5 hours
content
Feb 2024
last update
$59.99
regular price
What you will learn
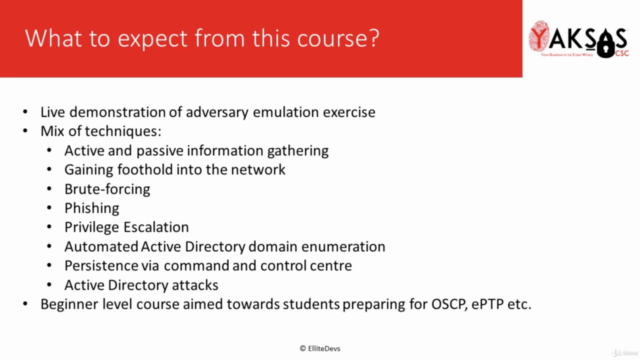
How to plan and manage adversary emulation exercise
Difference between red teaming and adversary emulation
MITRE ATT&CK Framework
Red team operations attack lifecycle
How to conduct adversary emulation exercise on a live organization
Open Source Intelligence (OSINT) techniques to gather information
Weaponizing exploits to gain foothold into the network
Password brute-forcing using custom generated lists
Phishing an employee
Escalating Privileges on Linux and Windows systems
Active Directory enumeration using BloodHound
Active Directory attacks
Establishing persistence via PoshC2 (command and control center software)
Creating an engagement report
Screenshots



Related Topics
3905220
udemy ID
3/10/2021
course created date
4/19/2021
course indexed date
Bot
course submited by